00:00:03And it gives you a clearer idea of the true meaning of the possession and send and exploration of digital currency.
00:00:08I’ll start with a brief overview of the first and advanced about the meaning of Alpetkoan.
00:00:12At Alpetkoan Johrh- is a digital file containing accounts and funds, and thus looks like a ledger.
00:00:17And keeps every computer in the network Alpetkoan a copy of this file.
00:00:21These figures do not represent anything in the real world.
00:00:24These numbers have a value only because people
00:00:26Ready to deal in goods and services in exchange for a higher number in their accounts.
00:00:29And they believe that others will do ideals,
00:00:31Where these numbers have a value only because we believe in it.
00:00:34This is no different from any other paper currency.
00:00:37If you want to send money, you want to broadcast in the network that you want to decrease the number in your account
00:00:40And the figure rises in the recipient’s account.
00:00:43Nodes are implemented (or computers) in the network Alpetkoan this transaction is in the version of the ledger
00:00:48Then send the deal to another contract.
00:00:51In addition to the above, some basic safety procedures based on mathematics, and that’s all of it!
00:00:54It is a system that allows a group of computers to maintain ledger accounts.
00:00:58This may seem similar to the way in which the Bank holds ledger accounts.
00:01:01But the existence of the ledger when a group of people rather than one institution leads to a set of important features.
00:01:07For example, you do not know anything about your position only when dealing with the bank.
00:01:11In Alpetkoan, everyone knows about all transactions that occur.
00:01:14You can trust your bank, or at least you can be paid if a bug has occurred.
00:01:18In Alpetkoan you are dealing with anonymous strangers so you should not trust anyone!
00:01:23Alpetkoan system was designed so tightly did not need any confidence!
00:01:26Where special protection everything in the system mathematical equations.
00:01:31And the rest of the video will explain in detail how can configure
00:01:33To allow a group of strangers to organize financial transactions for each other.
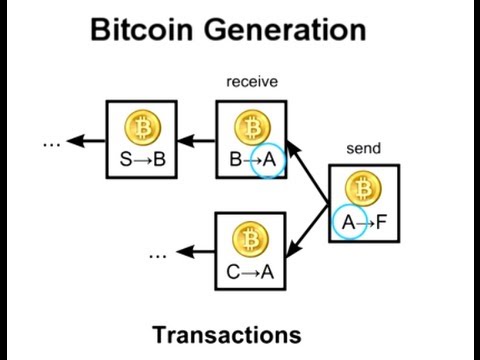
00:01:39Simply put, if it wants to “Alice” to send money to “Bob”
00:01:41Send a message containing the accounts and the amount of money you want to send.
00:01:44“Send 5 pieces of Alpetkoan from Alice to Bob.”
00:01:48Speaking after each node receives the message copied from the accounts book
00:01:51And then re-send this message to others.
00:01:53But how the contract to know that this request is false.
00:01:55Ie that the account holder is the one who sent the message.
00:01:58You need some sort of rules Alpetkoan passwords that allows you to send money
00:02:02This is called password digital signature.
00:02:05And it looks like it is written signature proves that the demand is false
00:02:08But it does so through a mathematical algorithm to prevent copying or fraud in the electronic Kingdom.
00:02:14This differs from the use of the word fixed password,
00:02:16Every deal you need a digital signature characteristic is different.
00:02:20Remember that you’re dealing with strangers so you do not show them any password Vinsguha or use them elsewhere.
00:02:27Digital signature by using two different keys works but linked.
00:02:31The first is a secret key to create a digital signature
00:02:33And the other key public can be used to verify the authenticity of the signature.
00:02:35It considered that the secret key is the real password
00:02:38The digital signature is the broker confirms that you have the password without having to show.
00:02:44Public key is used as the address of the addressee in Alpetkoan.
00:02:46When you send money to someone you send money to his key public.
00:02:51To send money, you have to prove that you are the real owner of the public key that pulled him money.
00:02:55To do so you have to create a digital signature by using the message container on the deal and the secret key.
00:03:00Can other contract in the network
00:03:01To use this signature in another function to verify that they are compatible with your key public.
00:03:06And allow the underlying mathematics behind the digital signature to confirm that the sender has the secret key without having to see it.
00:03:14Because the generation of digital signature depends on the message,
00:03:16The digital signature will be unique in each transaction.
00:03:18And therefore it can not be reused for another deal.
00:03:22This reliance on the message means that no one will be able to modify the message while sending in the network.
00:03:26Because any modification in the letter will make a false signature.
00:03:30Underlying mathematics behind this highly complex,
00:03:32And I will not try to explain it in detail now
00:03:34But I’ll give you some words that you can begin to look for:
00:03:37ECDSA and mathematical trap door.
00:03:42And I will explain more at the end of the video.
00:03:44So far we know that the digital signature is used to prove that the deal is forged,
00:03:48But I exaggerated the simplification of the mechanism that tracks through which the contract changes in account balances.
00:03:53In fact, the contract does not store account balances at all.
00:03:56But if you do not store the amount of money owned by each person,
00:03:59How do you know they have enough money to submit it to others?
00:04:02Instead of storing balances.
00:04:03Proving ownership of enough money by linking them with previous deals.
00:04:07And I will explain how this happens.
00:04:08To send Alice 5 pieces to Bob,
00:04:10They must refer to other transactions which received five pieces or more.
00:04:14These other deals are called “Palmdjulat”.
00:04:17Whereupon the other nodes to verify these inputs to make sure that this money is not received
00:04:22And that the total received greater or equal to five pieces.
00:04:26Let’s look at a real deal to see how this happens.
00:04:29This transaction refers to a total of six revenues 139.6 pieces.
00:04:34Note that the output contains two lines.
00:04:37The first restores the overflowing of the funds needed to the sender.
00:04:41Where the rule states that all the money in one of the inputs must be used in the whole deal.
00:04:46If you want to send the amount of money is not equal exactly the amount of money in the inputs that I referred to,
00:04:50You have to send any money to spare yourself again.
00:04:53And cross-reference to the inputs transferred ownership Alpetkoan in the chain-like,
00:04:58Where the legitimacy of a transaction depends on the legitimacy of previous deals,
00:05:02But how do you trust the legitimacy of these previous deals?
00:05:04Answer: You can not!
00:05:05And you have to verify the legitimacy of its revenues as well.
00:05:06In fact, after the inauguration of the program portfolio Alpetkoan for the first time,
00:05:09The program loads each deal has since the beginning Alpetkoan
00:05:12And then verify the legitimacy of one after the other until you can verify the legitimacy of the first deal was.
00:05:16Remember that you are dealing with strangers
00:05:18Therefore, it is necessary to verify the legitimacy of each transaction yourself.
00:05:21These scientific take more than 24 hours
00:05:23But you will not need it more than once.
00:05:25And after using one of the deals once
00:05:27This is the deal and disbursed can not be used again.
00:05:30And only one of them can be used one Mdjulath several times to refer to it in several deals.
00:05:35So the contract when you check the legitimacy of the transactions to ensure that its revenues have not acted before.
00:05:41To be frank, and for each income
00:05:43The contract realized from all previous transactions to make sure that this intake was not distracted by
00:05:49This may seem a waste of time
00:05:50Because there are more than 20 million deal now,
00:05:52But it is quick because of an index containing transaction is disbursed.
00:05:56If instead retain the contract book of accounts,
00:05:58They can track the huge list of deals.
00:06:01And owning a digital currency (configure)
00:06:02Means that there are deals to indicate your name on this list has not yet acted
00:06:06(Ie, did not refer to it Kmadjulat in other deals).
00:06:09One important and this property model results
00:06:11To know your digital currency
00:06:13Needs to pass through each transaction has
00:06:16Then collect all Mdjulatk is disbursed.
00:06:18And add to this important note:
00:06:20The system can support more complex than just sending money from someone else’s trades.
00:06:25You may have noticed the line is incomprehensible in the deal that we presented previously came out.
00:06:29Where the output is like the issue to be solved, rather than be a simple container consignees addresses.
00:06:33Instead of sending the money to be similar to sending the message,
00:06:35Sending money in Alpetkoan like putting money in a public safe
00:06:37And the issue of math lock must be resolved until you open the safe,
00:06:40Know the question of mathematics special programming language,
00:06:42And with that they are specifically designed to be solved by a single owner of the public key,
00:06:47There are many other possibilities.
00:06:49For example, we may need to signatures out of three to pass based on ensuring a third party transaction.
00:06:54And another example is the first deal has ever contained the question of which anyone can be solved.
00:07:00Most of the governor Alpetkoan hide from you this class code
00:07:03But you can be programmed with your own program that this has something to risk.
00:07:07More than 2,600 pieces have disappeared because of errors in the addresses in a range of deals.
00:07:13This emphasizes is important when dealing with Alpetkoan,
00:07:15Since you can not resort to a bank or credit card company
00:07:18Any errors by the user may lead to a permanent loss of digital blocks,
00:07:22This loss is not only limited to your account
00:07:23It is the loss of a full Alpetkoan economy.
00:07:26If you lose your secret
00:07:27Any funds linked to the corresponding public key will disappear forever.
00:07:31Since people often lose their keys
00:07:33For reasons such as hard disks crash and not back up,
00:07:36It means that the currency Alpetkoan will shrink with time.
00:07:41Before I talk about the latest technology and believes in the work of Alpetkoan is (exploration),
00:07:44I want to mention a few points about privacy when dealing Balbtkoan.
00:07:48If Alpetkoan entered through a network (Tor) that hide the IP address of thy,
00:07:52You can use Alpetkoan without showing anything other than the public key.
00:07:56To avoid the one to track all your transactions
00:07:58(Remember, all transactions are stored on all computers!)
00:08:01You can generate a new public key for each incoming deal.
00:08:05However it can be linked to these public keys accidentally.
00:08:09In the deal we have shown previously used six other deals as sources of money,
00:08:13And that with all these inputs received to different addresses
00:08:16They are all linked to the transaction.
00:08:18And the sender has demonstrated its ownership of all these titles
00:08:20Through the provision of electronic sign necessary to decode the lock each.
00:08:23The researchers used these links to study user behavior currency Alpetkoan.
00:08:27You may think that generate a public key to receive the funds may eventually lead to reveal the true identity,
00:08:32But even this step are confidential.
00:08:33And it can be done without an internet connection!
00:08:37Where simply press the custom button in the wallet program
00:08:39And the software will generate a public key and a special two new.
00:08:42Since there are many possibilities for these titles,
00:08:45There is no need to make sure that no other person has the same title.
00:08:48Compare this with the registration service for e-mail
00:08:50Where most of the names that you might consider them to be used in advance.
00:08:53In fact, if you can guess someone else will own all his money key!
00:08:57This is the number of all possible possibilities for addresses Alpetkoan.
00:09:00These massive numbers in several ways to protect Alpetkoan system.
00:09:03And it is useful to try to imagine the extent of magnitude,
00:09:07Some estimated the number of grains of sand on Earth by 7.5 million trillion,
00:09:13Now imagine that every grain of sand is another land full containing other sand,
00:09:17With this figure will remain much lower than the number of possibilities Alpetkoan addresses.
00:09:22Flanl_khas what we have learned about Alpetkoan security now.
00:09:24By ensuring the validity of the electronic signature.
00:09:26We know that the rightful owner is the only one capable of sending the deal
00:09:30To verify that the sender has enough money to spend.
00:09:33Check every income indicated to make sure that it is not an expense
00:09:36But there is still one loophole in the system
00:09:39This makes “verify that the transaction is disbursed” is not trusted.
00:09:41And this gap related to the order of the transaction.
00:09:44As the transaction moves from one node to another over the network,
00:09:47There is no guarantee that the order in which these deals received is the same as the order in which it was established.
00:09:52Do not trust registered on the transaction time
00:09:54Because the owner of the deal can easily lie about the time of the establishment of the deal.
00:09:57And therefore we have no way to know whether a transaction was established before the other
00:10:01This opens the door to fraud.
00:10:03A user can be cunning like Alice sends a deal that sends them his money to Bob,
00:10:07Bob and then wait until the goods shipped to him,
00:10:08And then sends another deal which refers to the same intake and return the money to himself.
00:10:13Because of the differences in the speed of transmission of the message,
00:10:14You will receive some of the network nodes in the second letter (in which the money was transferred to itself)
00:10:18Before the message where the money is spent on Bob.
00:10:20And when you reach the deal with Bob would be considered illegal
00:10:23As it tries to re-spending one earnings.
00:10:25Bob Vijsr this both of his goods and his money.
00:10:28The result would be contrary to within the network whether or not Bob owns this money
00:10:33Because of the absence of a way to prove that one of the deals came first.
00:10:36And therefore there must be a way to allow for the entire network to agree on the order of a transaction,
00:10:40And it is complex in a decentralized system.
00:10:44The solution in the Alpetkoan system is a smart way to ensure the protection and determine the order of occurrence of transactions
00:10:48And through some kind of racing sports.
00:10:51Arranges Alpetkoan system deals placing them in groups called blocs,
00:10:55And then connects these blocks with each other in so-called chain blocks.
00:10:59Note that it is different from the chain of transactions that we talked about previously.
00:11:02Where he used a series of blocks to arrange deals,
00:11:05While serving the chain of transactions to track the ownership of the funds.
00:11:09It is noteworthy in each block to the previous block,
00:11:11And this is what makes it one of the blocks other precedes chronologically.
00:11:14Where you can keep track of these signals about the past until you reach the first mass of transactions occurred.
00:11:19Ntabbar that deals in one block occurred at the same time.
00:11:22And called the deals that did not fall within the block after transactions is ranked or undocumented.
00:11:27Any node can be several deals not documented in the mass rally
00:11:30Then it suggests this block on the rest of the nodes in the network to be the new cluster in the chain.
00:11:35Because several people can establish several blocks at the same time,
00:11:38There are several possible new options as a bloc.
00:11:40How can the network to decide which blocks are the next in the series?
00:11:43We can not rely on the order of receipt of the blocks,
00:11:45As we explained earlier for deals,
00:11:47These blocks can reach different in the different nodes in the network order.
00:11:51Part of the solution is that each block must contain a distinctive mathematical solution to the issue.
00:11:57Where computers are used text content in the cluster to add random numbers Speculative
00:12:00To create the so-called “retail encrypted”
00:12:02Until you find the result is less than a specified value.
00:12:04Continued retail creates short as a result of any text, whatever its length,
00:12:08In our case the result is a record length of 32 bytes.
00:12:11Here are some examples of retail user continued in Altbekoan SHA256 system
00:12:17Notice how much output changes after adding one point at the end of the third example.
00:12:22No one can predict the output never
00:12:24Consequently, the only way to find a particular output is to carry out a random guess.
00:12:29This is like trying to guess the password to lock.
00:12:31You may be lucky in the first attempt,
00:12:33But you need a few guesses average.
00:12:36In fact, it may take a normal computer a few years to find true guesswork solves mass.
00:12:40All computers operate on a network Alpetkoan to guess the numbers,
00:12:43And thus find the solution takes an average of ten minutes.
00:12:47Broadcast the first to find a solution to the issue of mass mathematics
00:12:49And group transactions contained therein will become a new block in the chain.
00:12:54Random sports issue lead to a variation of the times when people find a solution
00:12:58Which reduces the probability to find two to resolve the issue at the same time.
00:13:02But several blocks at the same time may sometimes be resolved
00:13:06Which leads to the presence of several possible branches.
00:13:08In this case, you have to build on the first block you receive.
00:13:11Others may receive the blocks in a different order
00:13:14And each of them will be built on the first block received.
00:13:17And this node resolved when someone resolves the next block.
00:13:20And the base should always rely longer series are available.
00:13:24Make the possibility of solving math blocks at the same time weak.
00:13:27The probability of occurrence of several consecutive times weaker.
00:13:30And the result is that a series of blocks settle down quickly,
00:13:33This means that all agreed on the order of the blocks added to the end of the chain.
00:13:39Ambiguity at the end of the chain a significant impact on security transactions.
00:13:45For example, if you signed your deal in the short section in the series will lose its place in a series of blocks.
00:13:51This means that they will return to box undocumented transactions,
00:13:55It later becomes a new block components.
00:13:57Unfortunately, the deal opens up the possibility of losing their place in the chain to the door to the spending multiplier attack
00:14:02Which was the first reason we invented a system arrangement.
00:14:06Let’s see how it works spending multiplier attack in the system that described now.
00:14:10The conman (Alice) to send money to Bob.
00:14:13Bob is expected to document the deal in a series of blocks and then ship the goods.
00:14:19Now, and because the contract always choose the longest chain,
00:14:21If it can not generate the longest series in which the deal is replaced with Bob another deal with someone else,
00:14:26Erased his money from the chain.
00:14:29Bob will return a deal in principle to non-documented transactions.
00:14:32But since the deal is not replaced it with another which has spent the same intake,
00:14:36Bob contract deal will be considered invalid, because they rely on income already spent.
00:14:42How prevents the ranking system is not fool Bob?
00:14:46You may think that you can not pre-calculated series of blocks to the proposed network in a timely manner,
00:14:51But sports matter in each block to prevent such.
00:14:54Should we look more deeply on the encrypted hash continued that we talked about in advance in order to understand exactly why.
00:15:00As I mentioned previously,
00:15:01Cluster solution depends on trying to make the encrypted hash of the block output of less than a certain value.
00:15:06And do so through the experience of different random numbers at the end of the block.
00:15:10And output becomes a sign marked after be found this block (fingerprint).
00:15:15And change one character in the cluster will make retail output completely different,
00:15:20And so as we saw earlier when we add point.
00:15:26Using retail output, or footprint, to refer to the previous block.
00:15:31And therefore it can not replace the block in the middle of the chain because the hash value of the new block will vary,
00:15:38And the signal in the next block will not refer to it later.
00:15:41And the output is self-evident, but more importantly, one can not solve the block before we solve the bloc that precede them.
00:15:46And the reference to the previous block is part of the cluster text that enters the retail continued,
00:15:50And any change in it will need to be re-solution again.
00:15:53And to return to Alice,
00:15:54We are not aware can not calculate a branch in advance.
00:15:57You can begin to dissolve the block only if the cluster that you want to build on it Solved, and the retail value of the known.
00:16:03And therefore they are in a race with the rest of the network until the goods shipped Bob,
00:16:07And it is the time you want it not display the longest branch.
00:16:11And ask the question last one
00:16:11And you are Can not precede all if you own a computer supernatural speed,
00:16:16Or perhaps full of computer room.
00:16:18Even if possessed thousands of computers will not be able to profit from the race and mass solution,
00:16:22Because they do not race alone computers,
00:16:25But it raced the entire network.
00:16:27This is like a lottery game.
00:16:28Can use thousands of computers,
00:16:31Or to buy thousands of lottery cards,
00:16:33But even if it did, the possibility of profit for someone else remains high.
00:16:37It has to have more than half of computational power for the entire network
00:16:40To be her chance to dissolve the bloc by another person 50%.
00:16:44And it should have much more in order to have the possibility to solve several sequential blocks before the rest is greater.
00:16:48Protect deals in the series of blocks through a sports race,
00:16:52This race puts forward against the rest of the entire network.
00:16:55And result in the creation of new blocks over the old that the old blocks in the chain more secure.
00:17:01And the attacker must be preceded by the network for longer
00:17:03To succeed spending multiplier attack by replacing old ones block.
00:17:08The system exhibition spending multiplier attack near the end of the series,
00:17:12For this reason is advisable to wait until added a few new blocks
00:17:14Before it is considered the process of receiving final funds.
00:17:17One final note series blocks before I begin to explain another issue for Alpetkoan system.
00:17:22What is surprising that all the above and I explained does not need any confidence.
00:17:26If you receive information from strangers on the network,
00:17:29You can be sure that the blocks yourself solutions are correct.
00:17:32Because tough math problems, you are sure that there is no striker is able to manufacture himself.
00:17:38The existence of solutions proved to be caused by the computational capacity of the entire network.
00:17:43After that we talked about the mechanism of sending money through digital signature and chains deals,
00:17:47How protects the order of these deals in a series of blocks,
00:17:51Let’s talk about another topic: where it comes from coin Alpetkoan?
00:17:55You have to refer to an old deal where you’re the recipient before you can send money,
00:18:00But how these funds enter into the ownership chain at the beginning?
00:18:03The way through which generate and distribute the pieces at random,
00:18:06Award is to give each of finding a solution to the mass.
00:18:09For this so-called solution blocks “prospecting”
00:18:11With the primary aim is to document transactions and protect the chain blocks.
00:18:15Cut the prize every four years to half and in the end will not be created any new cut,
00:18:20There will be about 21 million pieces in the end.
00:18:23Remember that you can send the equivalent part of a million percent portion of the piece,
00:18:26And thus the limited number of pieces on our ability to use it will not affect.
00:18:30When the distribution of the awards depends,
00:18:32What are the incentives that will pay prospectors to handle deals?
00:18:35You can prospector receive with their prize any fees on deals
00:18:39Which can optionally be present within these transactions.
00:18:41Prospectors currently adds deals without fees in the blocks
00:18:45Because their primary goal is the prize after a mass solution,
00:18:47In the future, transactions will be dealt with mostly by fees attached to them,
00:18:51The deals that do not carry fees Vsijahlunha often.
00:18:54And therefore will not be sending money in free Alpetkoan,
00:18:56But we hope to be cheaper than the fees levied on credit cards.
00:19:01As I mentioned earlier, it would take a normal computer and the average number of years to resolve the block,
00:19:05And thus the chance of one individual to resolve any block before the rest of the network (which normally takes ten minutes) is very low.
00:19:12For a stable financial Ward,
00:19:14Many people join groups called Mines
00:19:16Which cooperate to solve the mass and resources are distributed based on the amount of participation.
00:19:21And is similar to that lottery cooperative groups,
00:19:24Except that some of these mines is very large, and make up more than 20% of the computers on the network.
00:19:30The presence of these large mines have a significant impact on safety.
00:19:35As we mentioned earlier, one attacker can not solve a series of sequential blocks before the rest of the network,
00:19:41But this becomes possible, and the probability of its occurrence increases the more computing capacity of the attacker compared with the rest of the network.
00:19:48And it has already managed one of the mines, union Alpetkoan, to replace the six blocks of sequential alone,
00:19:53It identifies the number of its affiliates voluntarily and in order to prevent the collapse of confidence in network Alpetkoan.
00:19:58Even with a high computing power,
00:19:59Whenever the deal earlier in the series, the more change more difficult by the attacker.
00:20:05Currently it recommended that you wait for one block, or get a closer one, before the transmission is considered final.
00:20:12And for the great deals, wait six blocks at least.
00:20:15And with the ability of union Alpetkoan six sequential blocks solution you’ll probably have to wait more.
00:20:20The blocks are designed so that you need ten minutes to solve,
00:20:23So you have to wait a full hour to solve 6 new blocks.
00:20:26If you compare it with the few seconds it takes to send a deal via credit card,
00:20:29You’ll find all this waiting period to document the deal is troublesome,
00:20:32But remember that credit card users can call steal their card after several months
00:20:36And to restore their money from the merchants,
00:20:39And therefore Alpetkoan much faster than the point of view of the merchant.
00:20:42The choice of ten minutes was randomly,
00:20:45But too little will lead to instability,
00:20:48And long time will lead to the postponement of documenting transactions.
00:20:50And join with the largest number of computers to the network,
00:20:52With the hardware design software dedicated to the exploration,
00:20:55Will decrease the time needed to resolve the block.
00:20:58And to compensate for it,
00:20:59Re-evaluation of all programs Alpetkoan difficult math problems every two weeks
00:21:02So it takes ten minutes to solve.
00:21:04Conversely, there is another digital currency called the Aatkoan was able to operate time of 2.5 minutes for each block.
00:21:12In summary, Alpetkoan is a digital coin protected mathematics
00:21:15And it works to save users on the network.
00:21:18The digital signature gives individuals the right to conduct transactions,
00:21:21And transferred ownership across the chain of transactions,
00:21:23And saves the sequence of occurrence of transactions arranged in a series of blocks.
00:21:27And a request to resolve the issue of mathematics for each block,
00:21:30Put the attackers in the competition can not be Arbhoha against the rest of the network.
00:21:36The future Alpetkoan many creative ideas,
00:21:38Such as preventing government intervention and reduce financial secrecy and transfer fees.
00:21:44There are many challenges faced, such as the difficulty of sharing Alpetkoan with other currencies,
00:21:49And was a classification refuge for illegal acts and tax evasion,
00:21:53So governments may try to prevent them.
00:21:54In addition, the mathematics race series which protects the blocks consumes a large amount of electricity.
00:22:00If you want to read a written copy of the video
00:22:02You can drop my blog,
00:22:05imponderablethings.com
00:22:07The Code contains additional explanations for the underlying mathematics behind the digital signature and encrypted hash that support the system.
”